This post contains reports from two Columbia Journalism School students who attended Bellingcat’s five day Open Source / Digital Research Training Workshop, hosted by Graphika, Inc. The workshop taught students how to conduct investigations into online information sources such as social media feeds, satellite imagery, and user-generated videos. Bellingcat, founded by Eliot Higgins, is known for pioneering this form of online inquiry, dubbed ‘open-source investigation’, which he originally used to investigate Syria’s use of chemical weapons in 2012. Touting its origins in citizen journalism, in part due to its low barrier to entry, open-source investigation is being used by an increasingly large group of research organizations and journalists, and will likely continue to grow in popularity as more information streams are hosted on the web.
In the first blog post, Isaac Schultz uses Bellingcat’s toolkit to explore what “people can tell you without realizing it” – using the simple case of vacation tweets. The second post is by Joasia E. Popowicz who uses the methods she learned from Bellingcat to determine if Russia has moved planes capable of carrying nuclear weapons to its base in Crimea. Jump down to it.
Reflecting on the Bellingcat workshop could take many forms. I could write about how I spent two days figuring out whether there were nuclear-capable Tupolev 22-M bombers in the Crimea, detailing every social media account and geospatial search I conducted along the way. I could mention @princess_0605, the Russian wife of a bomber pilot whose one Instagram photo from 2016 greatly informed the investigation’s effort. I could describe the toolkit I now possess at length, and easily go over the 750-or-so words requested for this reflection. I’d rather do the following.
By Isaac Schultz
My first contact with Mark Hansen during Spring Break was the image below, emailed to me on 3/22/19 at 6:30PM.
Not so informative, you might think.
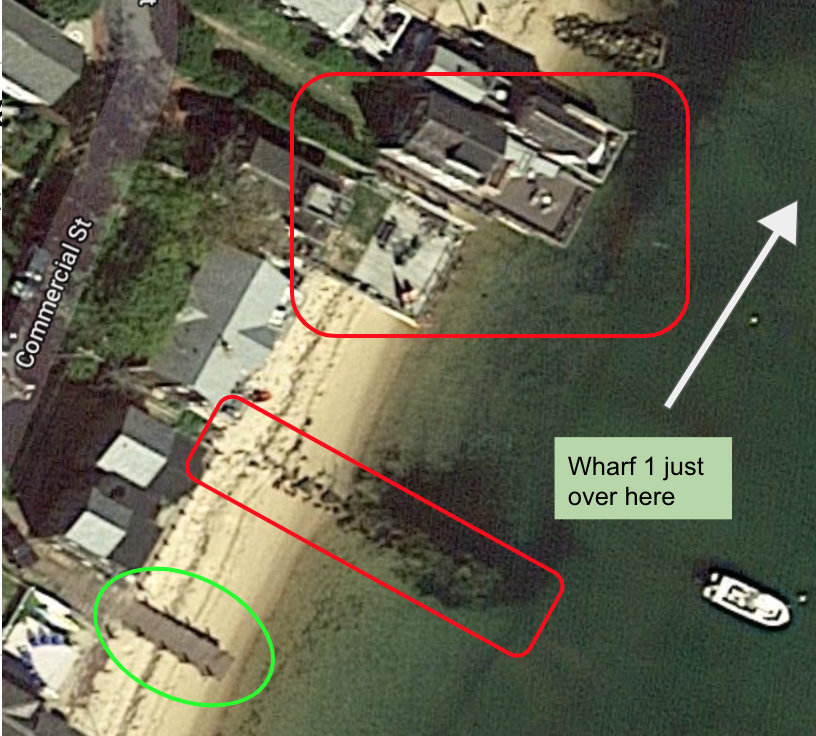
Actually, even without the EXIF data, it is a fairly simple image to geolocate. According to Twitter postings at his Twitter handle, @cocteau, Hansen was vacationing in “ptown,” or Provincetown, MA. Looking at satellite imagery of Provincetown, there are only 3 candidates for the wharf in the image.
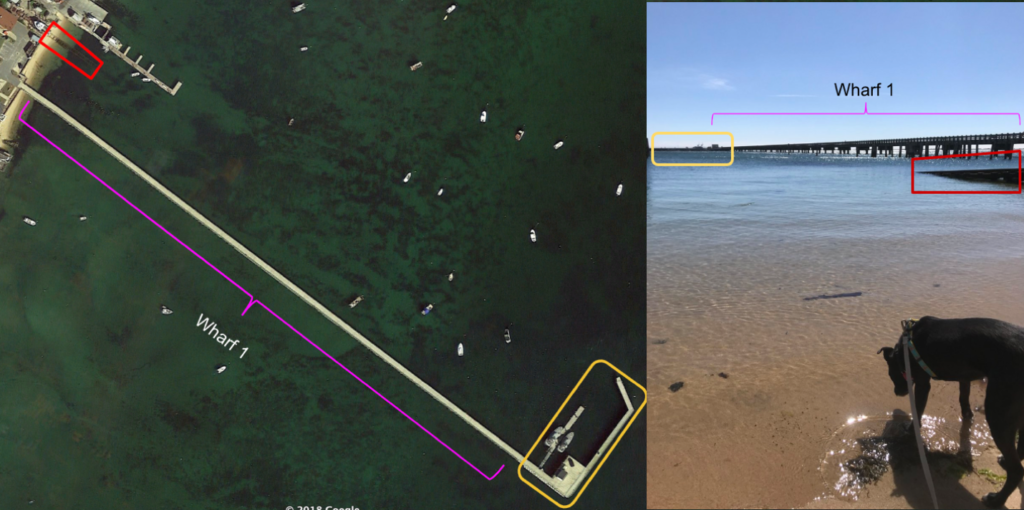
Wharf 1 has a distinctive pattern of support beams – stiltlike supports, followed by two parallel beams, and then a crosshatched set of beams. Corroborated by a public image shared via Google Maps, Wharf 1 looked to be it. Noting the wooden surface beneath Tig, we can isolate a structure south of wharf 1 with some docklike features.

Three buildings look to have barriers around their decks, so I eliminated them. Another structure looks to be a stone jetty. Thus, only one candidate remained: a wooden dock to the South.
But to corroborate this (maybe there are other docks that look this way? Maybe Hansen was lying on Twitter about where he was?), we look at some other images he shared on Twitter:
The left image is easy enough. There is a prominent wooden building on the dock in the distance, and the jetty behind the dock gives some contextual information. The building to the left shows that the field of view was obstructed; otherwise, the entire wharf would have been visible.


Now, the final photo. This post gives us two photographs, helpful for a quick geolocation. We can identify the wharf as the same one in the previous images. Though the pattern is harder to distinguish, the left photo shows how it turns in an “L” shape, and the sloping structure on the right of the picture shows us Hansen was north of the wharf when he took it:
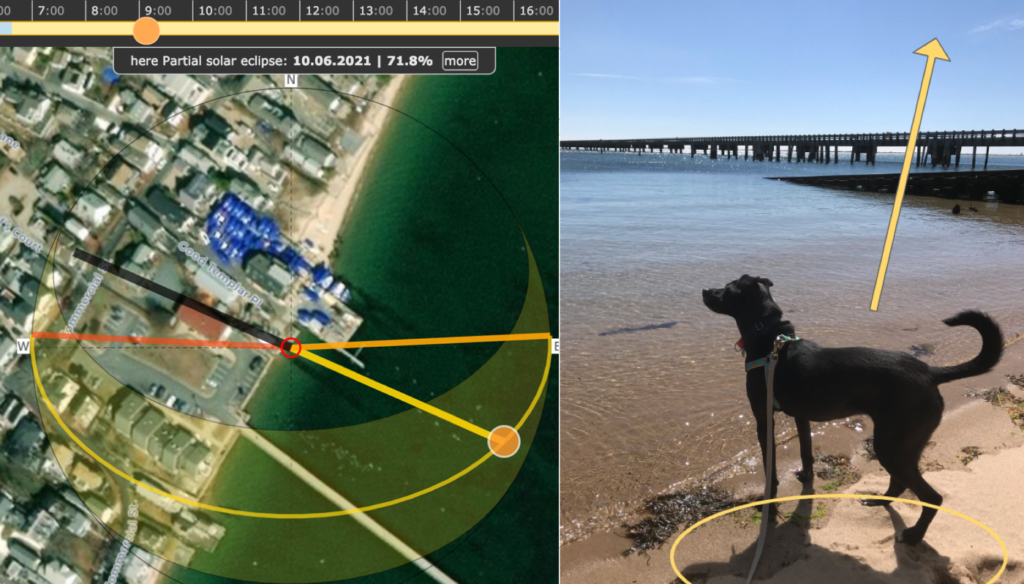
So all that’s easy now, thanks to Bellingcat (and a reckless mention of “ptown.”) But what about when the photo was taken? Was it snapped just past 9am, when it was posted to Twitter? To do this, we use a handy online shadow calculator and make use of Tig’s shadow:
Honestly, it looks a little hard to tell for me. So there’s room to improve. But it’s certain that the photo wasn’t taken after 2pm or before 8am. Voila! I know where you were, precisely. And around when, at least in one case.
The Bellingcat workshop was everything I could’ve wanted. I met some great people in fascinating lines of work, and have since been thinking up better ways to surveil subjects of inquiry and fact check basic information. I used to think EXIF data was the best way of “hacking” someone’s security, but there is so much people can tell you without realizing it. When used in conjunction with social media enquiries, the geolocation work can reveal much about peoples’ whereabouts and activity.
I think many stories can be told through digital investigation, and I previously didn’t think much of their utility beyond breaking news stories. But being able to cross-reference open-source platforms gives the journalist an opportunity to recreate scenes from the past, as they happened, or put someone’s contemporary account of an event up to scrutiny.
Whether it’s your professor’s spring break trip or a humanitarian crisis in Somalia, open-source investigation is possible anywhere in the world. That’s part of what makes it so useful – if you have a computer and the know-how, you can have a significant impact.
Is Russia moving Tu-22M3s to Crimea? A Bellingcat workshop hosted by the Brown Institute at Columbia gave me the tools to investigate.
By Joasia E. Popowicz.
Bellingcat, the open source investigative unit made up from contributors from all around the world, has had a hand in reporting on clashes on the Venezuelan border, the downing of the MH17 aircraft, in collaboration with The Insider and McClatchy DC Bureau, and most recently, Russian aircraft presence in Venezuela (below).

Open source means publicly available data, which Bellingcat leverages with innovative cross-platform search techniques to use in its investigations.
A workshop in March 2019 at the Brown Institute in Columbia University, New York, brought together security analysts, journalists and U.N. staff to learn how to advance their investigations. The Brown institute at the Columbia Graduate School of Journalism is a joint collaboration with the Stanford School of Engineering to promote media innovation.
Led by Aric Toler, the five-day Bellingcat workshop had three days of intensive training covering geo and identity verification, as well as tracking using satellite imagery, followed by two days of supported inquiry into independent projects.
Geo verification is the scientific art of using clues from satellite imagery and the environment, such as the sun’s position, to pinpoint the exact coordinates of an event. Identity verification includes analyzing image authenticity using its metadata and reverse engineering its origins. Tracking includes looking at flight paths and combining social media information to triangulate data points and map individuals’ locations. Bellingcat’s open source toolkit can be found here.
After three days practicing, we turned to our individual projects.
These included tracking associates of corrupt African officials, identifying a hacker stealing credit card details and geolocating the site of human rights atrocities.
Earlier that week there were conflicting reports about the extent of Russia’s nuclear capabilities in Crimea: by March 19, 2019, reports came through from the Tass Russia News Agency that Russia both had and hadn’t moved Tu-22M3s to the Gvardeiskyy air base in Crimea.
My group decided to apply our new skills and investigate.
Crimea was annexed from Ukraine following the Maidan revolutions in 2014, which saw pro-Russian president Yanukovych flee with help from Putin. Russia already has nuclear capabilities in the region, but presence of Tu-22M3 would indicate an expansion.
On Monday March 18, 2019, Russian Senator Viktor Bondarev, head of the national defense committee of Moscow’s upper house of parliament said Russia had deployed Tupolev Tu-22M3s to the Gvardeiskyy air base. The next day, Vladimir Shamanov, head of the lower house of the parliament’s defence committee, reportedly directly contradicted Bondarev’s claims.
Tu-22M3s aircraft, the same one’s which Russia used to attack targets in Syria, are capable of carrying nuclear warheads and moving Tu-22M3s to Gvardeiskyy would extend Russia’s combat range to encompass more of the Middle East and Northern Africa.
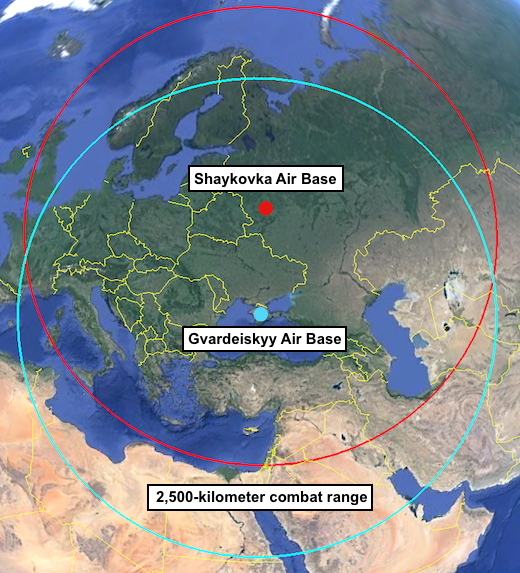
So are there or aren’t there Tu-22M3s in Crimea? It’s a Mueller maybe. Here’s what we found:
Our analysis included videos from Youtube of weapons being transported into Crimea, identifying Russian military personnel and analysing content uploaded to Instagram, Twitter and VK, the Russian social media equivalent of Facebook, as well satellite imagery of Gvardeiskyy and reports concerning the closest viable nuclear storage facilities.
We were limited by the time frame of the latest available satellite imagery on Google Earth. Images of the Gvardeiskyy air base showed no TU-22M3s but these were from January 2018.

Digital Globe and Sentinel had more recent images but the resolution was too low to confirm aircraft types.

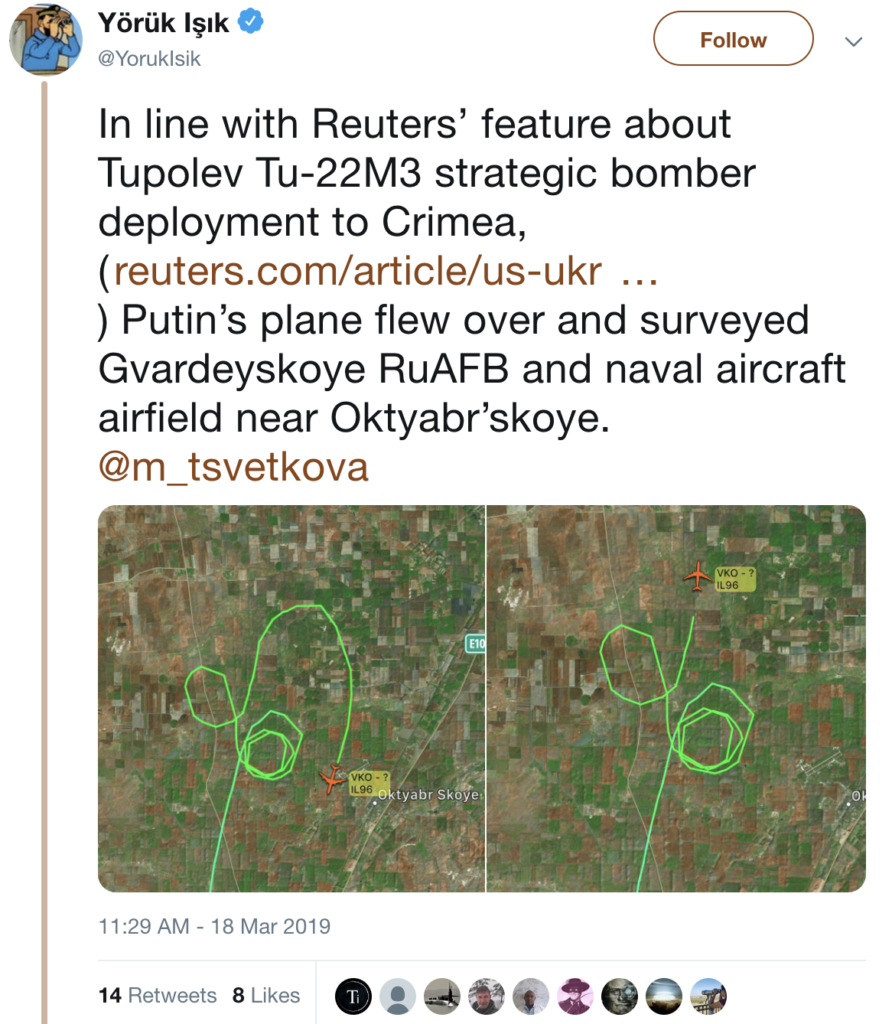
Yörük Işık (@YorukIsik) did however record Putin’s flight path on March 18, 2019, from Moscow to Crimea, circling the Gvardeiskyy airfield. Putin was travelling to Crimea to mark the five year anniversary of its annexation.
Meanwhile, the military camp at the location of the nearest national-level storage facility, according to Hans M. Kristensen, director of the Nuclear Information Project at the Federation of American Scientists, was getting a revamp last year.

So we couldn’t determine for certain that Russia Tu-22M3s are now at Gvardeiskyy in Crimea.
We did find Putin’s plane was circling the airbase on the day he was traveling to celebrate Russia’s annexation of Crimea, and work has reportedly started on the military base at the nearest nuclear storage site in Belgorod. To be continued.
At Columbia Journalism School, I’ve been trained in investigative techniques as part of the Toni Stabile Investigative specialization and coding, to collect content to store in remote servers, as part of the computational journalism course spearheaded by Mark Hansen. Together with the tools learnt on the Bellingcat workshop, I look forward to applying these in my investigations.
Thank you to the Bellingcat team and Mark Hansen, director of the Brown institute, for organizing the workshop.